CLI User Access Levels
Each command offered through the Solace Event Broker CLI has a particular scope and access level requirement. CLI users can use a command offered through the CLI only if that user’s configured access levels are sufficient for the scope of the command.
Access levels are assigned to each CLI user account to control what types of commands the user is allowed to execute. The following access levels are available:
- none
- read-only
- mesh-manager
- read-write
- admin
The CLI user cannot execute CLI commands except for a few that pertain to the log in and display preferences for the user’s own account.
The CLI user can execute CLI commands to display operational information about the event broker but cannot change its configuration. A monitoring application would typically use a read-only access level.
The CLI user can execute CLI commands to both display operational information about the event broker and perform some event broker configurations—including all aspects related to client connectivity, mesh connectivity, and client security features. This access level is useful for users that need access to these commands, but are not allowed global read-write access. A management user responsible for administering an event mesh would commonly be granted a mesh-manager access level.
The CLI user can execute CLI commands to both display operational information about the event broker and perform most event broker configurations—including creating other CLI user accounts with access levels of none. A management user responsible for configuring the event broker or Message VPN services would commonly be granted a read-write access level.
The CLI user can execute all CLI commands on the event broker. This includes controlling event broker-wide authentication and authorization parameters and creating other admin users. (This access level can only be applied to global-scoped commands.)
For detailed information about the capabilities offered at each access level, refer to CLI Command Access Level Capabilities.
CLI Command Scopes
CLI users can be configured to manage the entire event broker and/or a subset of Message VPNs. To permit this level of control, each CLI user account is assigned access levels for the following different scopes:
- global
- Message VPN
A global access level dictates what the user is allowed to do across the entire event broker.
One or more Message VPN access levels dictate what the CLI user is allowed to do within Message VPNs.
An assigned Global access level is all-encompassing and takes precedence over the Message VPN access level. It gives a CLI user the same level of access for all CLI commands, including those that have a Message VPN scope. To configure, see Configuring Global Access Levels.
In addition to a global access level, Message VPN access levels are assigned so that users with none or read-only global access levels can be granted increased access to Message VPN-scoped CLI commands, as required. An assigned Message VPN access level can only increase–not decrease–the Message VPN access level that a CLI user effectively receives from its assigned global access level. The Message VPN access levels can be assigned through:
- The default Message VPN access level
- Message VPN exceptions
This provides a consistent Message VPN access level across all provisioned Message VPNs. A default Message VPN access level is always assigned to a CLI user, but it only affects a CLI user’s access to Message VPN-scoped CLI commands if it is greater than the user’s assigned global access level. For more information, see Configuring Message VPN Default Access Levels
These are per-Message VPN exceptions to the default Message VPN access level. These exceptions can either increase or decrease the assigned default Message VPN access level for the specified Message VPN. For more information, see Configuring Message VPN Access Level Exceptions
Assigning both global-scoped and Message VPN-scoped access levels allows the appropriate access to be granted to users based on their administrative roles. Consider the two following examples:
- A system‑wide administrator could be assigned a global access level of admin, which allows that user to run any command on the event broker, whether it is a global-scoped or Message VPN-scoped command.
- A user who needs to monitor operational statistics within a Message VPN could be assigned a global access level of none and a Message VPN access level of read-only for that Message VPN.
For security reasons, only a few administrators should be given access to CLI user accounts with global access levels of read-write or admin. In general, Message VPN-scoped CLI commands contain the message-vpn keyword, or they are contained in a CLI mode with the message-vpn keyword. For example, commands to configure client usernames, durable endpoints, and Distributed Caches are created on a per-Message VPN basis:
solace(configure)# client-username <username> message-vpn <vpn-name>
solace(configure/client-username)# acl-profile <name>
...
solace(configure)# message-spool message-vpn <vpn-name>
solace(configure/message-spool)# create queue <name>
...
solace(configure)# message-vpn <vpn-name>
solace(configure/message-vpn)# distributed-cache-management
Assigning Access Levels
For information on assigning access levels, refer to Configuring Default CLI User Access Levels with External Authentication.
Creating and Managing CLI User Accounts
Your ability to create and delete user accounts, and to change the access levels and passwords of existing user accounts, depends on the global access level of the user account you use. The general limitations for each global access levels are as follows:
- A CLI user with a global access level of admin can create, delete, or make changes to other CLI user accounts without any restrictions.
- A CLI user account with a global access level of read-write can:
- only create or delete other CLI user accounts with a global access level of none
- set a Message VPN access level for any CLI user account
- change the password for its own user account and user accounts with an access level of none
- A CLI user account with a global access level of mesh-manager, read-only, or none can only change the password of its own user account.
When access level and password changes are made to a CLI user account, they do not affect any active sessions that are using that user account. The changes only take effect the next time a user logs in to that CLI user account.
For more information on the specifics of CLI user account configuration, refer to Configuring Internal CLI User Accounts.
CLI Command Access Level Capabilities
There are multiple possible global access levels and Message VPN access levels that can be assigned to a CLI user with various capabilities and limitations.
CLI users only see commands that they are authorized to execute. This means, for example, that Help commands will not show unauthorized commands, and CLI tab‑completion will not complete a command for which the user is not authorized. In addition, wildcard characters used in CLI commands will not allow a user to see or access network resources, such as Message VPNs or client profiles, that they are not authorized for.
To determine the minimum access level required to execute a command, you can look up the command used to define or set the configuration parameter in the Solace Event Broker CLI Command Reference. In the displayed help for the command, a MINIMUM REQUIRED SCOPE/ACCESS LEVEL: section lists the required access level.
solace(admin/cspf)# neighbor ?
COMMAND:
neighbor <physical-router-name>
DESCRIPTION:
Enter neighbor admin mode
MINIMUM REQUIRED SCOPE/ACCESS LEVEL:
global/mesh-manager
PARAMETERS:
<physical-router-name> - [1..64 chars] Physical Router name of the
neighbor; may contain wildcard characters *
and ?
Or you can see the CLI Commands Scope and Access-Level Requirements section for a list of all commands and their required access level.
Global Access Levels
The table below provides information on the possible global access levels that can be assigned to a CLI user and many of the capabilities and limitations that those access levels present.
| Level | Capabilities and Limitations... |
|---|---|
|
none |
The CLI user has access to minimal CLI commands, and no jail file system access. However, a CLI user with this global access level can:
CLI users with a global access level of none can be given additional access to Message VPN commands by assigning them a default Message VPN access level of read-only or read-write or a Message VPN access level exception of read-only or read-write. |
|
read-only (The default value for the global access level.) |
In addition to the capabilities offered by a global access level of none, a CLI user with a global access level of read-only can:
CLI users with a global access level of read-only can be given additional capabilities at the Message VPN level by assigning them a default Message VPN access level or a Message VPN access level exception of read-write. |
|
mesh-manager |
In addition to the capabilities offered by a global access level of read-only, a CLI user with an access level of mesh-manager can:
CLI users with a global access level of mesh-manager can be given additional capabilities at the Message VPN level by assigning them a default Message VPN access level or a Message VPN access level exception of read-write. |
|
read-write |
In addition to the capabilities offered by a global access level of mesh‑manager, a CLI user with an access level of read-write can perform most configuration changes, including:
|
|
admin |
The CLI user has full access to all global and Message VPN-scoped CLI commands (it provides an effective Message VPN access level of read-write). Some configuration changes or actions that can only be performed with a global access level of admin include:
|
VPN Access Levels
The following table provides information on the possible Message VPN access levels that can be assigned to a Solace Event Broker CLI user and many of the capabilities and limitations that those access levels present.
| Level | Capabilities and Limitations... |
|---|---|
|
none (The default value for the default Message VPN access level.) |
The CLI user has no access to Message VPN-scoped CLI commands. |
|
read-only |
The CLI user can:
|
|
read-write |
In addition to the capabilities offered by a Message VPN access level of read-only, a CLI user with a Message VPN access level of read-write can perform most Message VPN scoped configuration changes. Some of configuration changes or actions that are forbidden (and would require a higher global access level of read-write or admin) because they affect system resources include:
Global system administrators are expected to create client profiles that define how clients within a Message VPN are expected to behave. However, a CLI user limited to Message VPN scope does have access to show client profiles and assign client profiles to client username objects. |
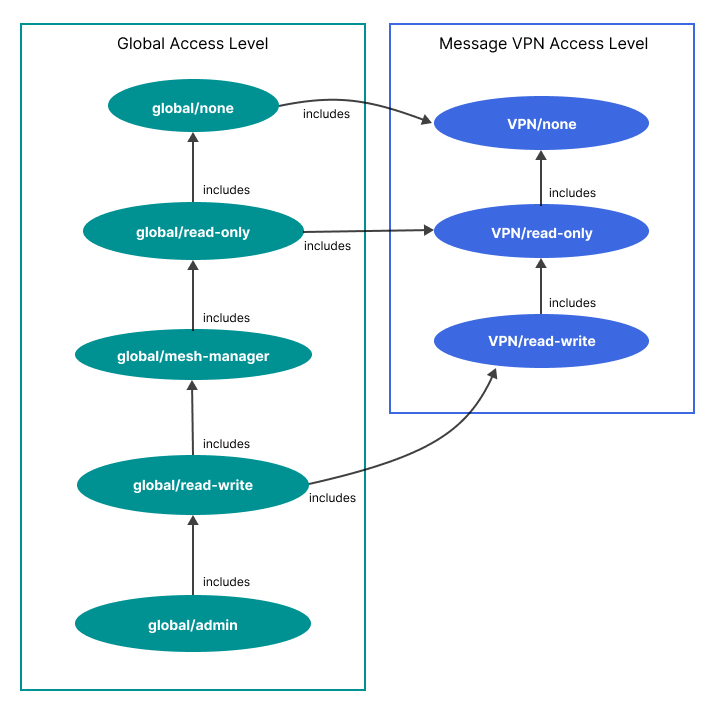
Access Level Relationships
The following diagram summarizes the relationships between each access level. More specifically, it shows how each access level includes the permissions from the previous access level and it also shows the Message VPN access level permissions that are included in each global access level by default.