Deploying and Managing Agent Mesh Manager
Solace Agent Mesh Manager provides a managed service that enhances your Solace Agent Mesh implementation. Agent Mesh Manager is fully hosted and managed by Solace. Solace handles provisioning, lifecycle management, infrastructure, and access control for you.
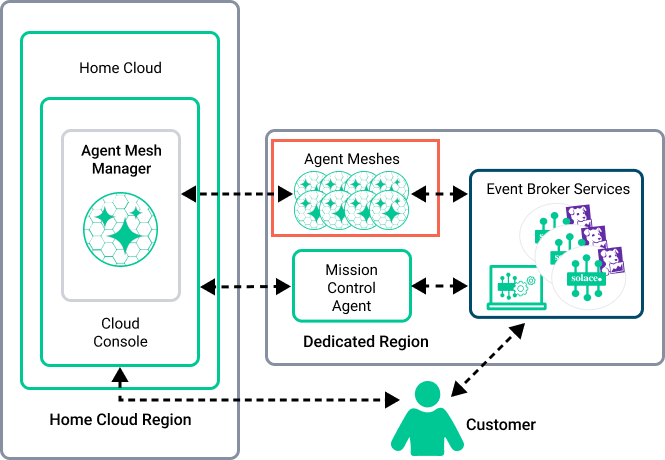
The Early Access (EA) version of Agent Mesh Manager requires that your agent meshes and the event broker service they connect to reside in a Dedicated Cluster in Solace Cloud. For more information about Solace Cloud networking options and connectivity, see Networking Options for Dedicated Cluster Deployments.
Architecture and Deployment Model
Solace Cloud acts as the control plane for agent mesh instances, managing some aspects of your deployment, including:
- Agent Mesh upgrades
- infrastructure provisioning and scaling
- certificate and DNS management
- monitoring agent mesh service health
- persistence layer (PostgreSQL, Amazon S3-compatible object store)
You are responsible for managing:
- integrations with external systems, including your identity provider (IdP)
- user role assignment and single sign‑on (SSO) enablement
- all agents, workflows, gateways, and other components in each agent mesh instance
The following diagram illustrates how Agent Mesh Manager and your agent meshes fit into the Solace Cloud architecture.
Agent Mesh Connectivity in Solace Cloud
Solace Agent Mesh connectivity requirements are based on the existing Solace Cloud Connectivity Model for Kubernetes Deployments.
Agent Mesh has a few additional connectivity requirements to consider. In Solace Cloud it is a Solace‑managed service that runs in Solace‑managed Kubernetes clusters and connects to your event broker services and external systems. From a networking perspective, Agent Mesh Manager in Solace Cloud introduces:
- a Solace Agent Mesh endpoint (HTTPS) used by users and integrations to access the Agent Mesh web interface and APIs
- outbound connections from the agent mesh to:
- the connected event broker service
- AI model providers.
- external systems used by agents and gateways
- an IdP if SSO is enabled
Operational Connectivity Considerations
Agent mesh instances are deployed in Solace‑managed Kubernetes clusters. Solace configures the operational connectivity that is required for these deployments. All target connections initiated by Solace Agent Mesh must be reachable from the Dedicated Cluster.
These connections are part of the same operational connectivity envelope as the Mission Control Agent and monitoring components. Solace provisions and manages these requirements. You do not need to open additional ports beyond those already documented in Connection Requirements for Solace Cloud Components .
Messaging Connectivity Considerations
Each agent mesh is associated with a specific event broker service and must be able to establish a messaging connection to the event broker service using (SMF) over TLS.
Solace recommends configuring private connection endpoints on the event broker service to allow agent meshes to connect using a private IP address. If the event broker service has both public and private endpoints, the agent mesh connects using a private endpoint. Agent meshes connect using a public endpoint only if a private endpoint is not available.
Solace provisions a Solace Agent Mesh endpoint for Solace Cloud that allows access to an agent mesh from your browser and from external systems that call Solace Agent Mesh REST APIs and integrations. The endpoint is an HTTPS URL using port 443. It is typically exposed through a load balancer that routes traffic to Agent Mesh services in the Kubernetes cluster.