Central Monitoring Service and Insights Agents
Solace Cloud uses a central monitoring service to collect monitoring data (statistics/metrics) and logs from event broker services. The central monitoring service stores the information. Operational monitoring metrics, statistics, and logs are centrally monitored from the Solace Home Cloud. Microservices that are part of the Home Cloud communicate with the central monitoring service to retrieve reports and data regarding the event broker services. The central monitoring service is Datadog. Datadog is a third-party service that provides a secure solution built on a highly reliable stack for collecting and storing information that's SOC2, Type I and SOC2, Type II compliant. The SOC2 reports are available on the Datadog website.
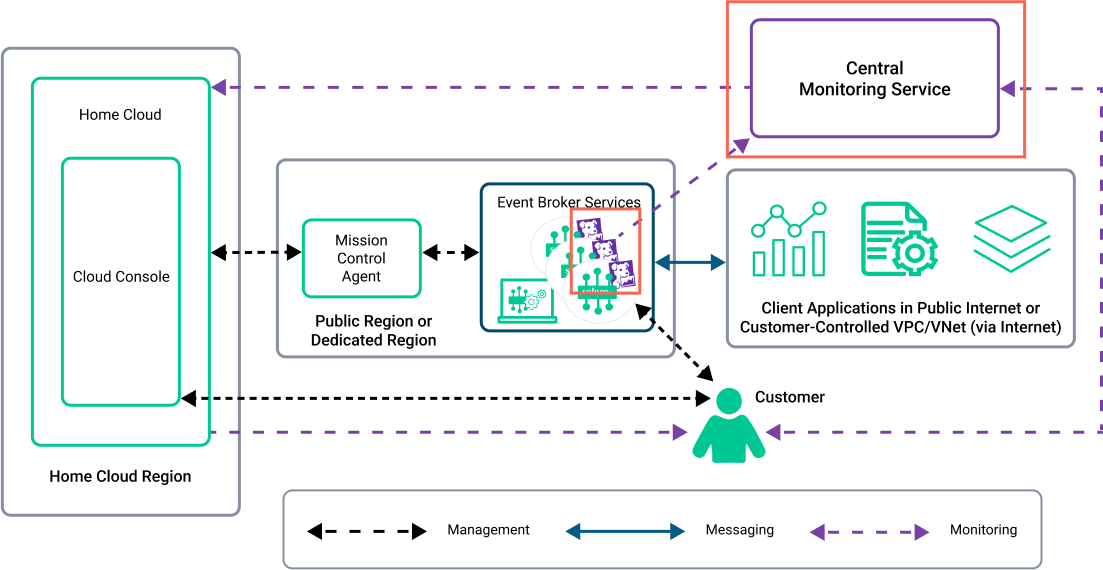
Insights Agents are configured by the Mission Control Agent to send monitoring data and logs about event broker services to the central monitoring service. Each event broker service has an Insights Agent configured. In the following diagram, the red box highlights the Datadog agents and the central monitoring service:
Insights Agents collect only system-level information and metrics required to monitor and manage the event broker services. The system-level information and metrics do not contain any personal-identifiable information – only monitoring data about the event broker services. The information exchanged between the Insights Agents and the central monitoring service is encrypted using TLS 1.2 or TLS 1.3. For more information about the data collected, see Log Information Collected.
The data that is sent to the central monitoring service does identify the event broker service and its event brokers. Since Solace Cloud is a SaaS offering, this required system-level information is vital to monitor the health of the event broker services running in your deployment.
The data collected by the central monitoring service is also accessible with an Solace Insights subscription. You can use Insights to monitor the performance of client applications, see statistics about your event broker services, and receive notifications. Advanced visualizations are also available from a separate, Solace-provided Datadog account. For more information about Solace Insights, see Insights Overview and Solace Insights Advanced Monitoring.
Central Monitoring Service Connectivity
For Datadog to receive monitoring traffic it requires a number of public IP addresses to be allowed to send this monitoring traffic from your deployed event broker services. For Solace-controlled (Public Clusters and Dedicated Clusters) deployments, this connectivity is configured by Solace. For Customer-Controlled Clusters, you (or a network administrator in your organization) must enable this connectivity. One way enable the traffic flow is to add and maintain the list of IP addresses in your network that send traffic to the central monitoring service. To get the list of IP addresses, see Getting the IP Addresses for Monitoring Traffic.